Smooth sailing for cloud transformations
Migrating code, applications, and assets to the cloud create new weaknesses for cybercriminals to exploit. Prevent data loss, unauthorized access, and compliance risks by calling on a million-strong community of security researchers with the expertise to find vulnerabilities scanners and AI miss.
Your cloud security special forces
Use ethical hackers on critical assets like cloud applications and APIs, where scanning tools may be inadequate.
See vulnerabilities more clearly.
Score vulnerabilities using Common Vulnerability Scoring System (CVSS) to create a common language around the severity of bugs, allowing consensus among multiple stakeholders.
Score vulnerabilities using Common Vulnerability Scoring System (CVSS) to create a common language around the severity of bugs, allowing consensus among multiple stakeholders.
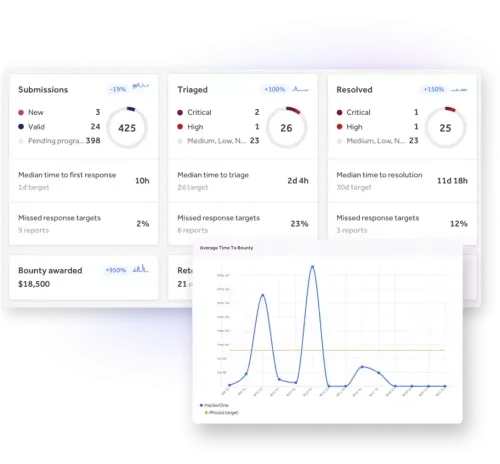
Dial down risk, noise and cost.
Cloud-first organizations need continuous security monitoring to expose vulnerabilities, identify remediation strategies, and increase operational efficiency.
Cloud-first organizations need continuous security monitoring to expose vulnerabilities, identify remediation strategies, and increase operational efficiency.
Get a built-in risk forecast.
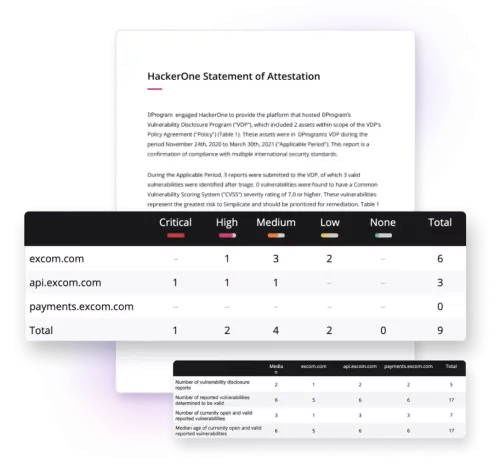
With built-in visibility and reporting, you can assess cloud security risks before they disrupt your business or cast a shadow over your brand.
With built-in visibility and reporting, you can assess cloud security risks before they disrupt your business or cast a shadow over your brand.
Dynamic, compliance-ready threat response
Ongoing vulnerability assessments are critical to keeping your cloud applications safe. With AWS-specific pentesting, you can minimize risk to your AWS cloud applications by accessing AWS Certified ethical hackers to find and fix vulnerabilities fast.
- Gain real-time visibility into threats to your AWS applications. Go beyond traditional pentests with compliance-ready reports to satisfy SOC 2 Type II and ISO 2700.
- Identify security gaps as you move to the AWS cloud, significantly reducing the risk of an exploit.
- Minimize vulnerabilities across your cloud applications, so you don’t put your customers at risk.
Rise above your cloud vulnerabilities.
The only sure way to protect your cloud applications? Find weak points before bad actors do. A vulnerability disclosure program lets the public alert you to hidden problems—helping you meet compliance mandates and build trust with your customers.
- Implement a vulnerability disclosure policy to comply with regulations while arming security operation teams with vulnerability intelligence.
- Identify security gaps as you move to the cloud, significantly reducing the risk of an exploit.
- Minimize vulnerabilities across your cloud applications so you don’t put your customers at risk.
Harden your cloud attack surface.
Jumping from console to console to keep up with cyber risks in the cloud can leave your organization open to attack and overload your teams. You need a consolidated security platform.
- Unify vulnerability findings from multiple sources into a single solution with customized workflows.
- Minimize the risk of a cyber attack by inviting ethical hackers to vet your application security.
- Detect cloud misconfigurations to prevent costly exploits.